Co-Sourcing vs Out-sourcing: a strategic decision that will define your audit function’s relevance in 2026 and beyond
Layoffs are reshaping corporate structures overnight. Regulatory frameworks are tightening across every industry. Emerging risks — from AI governance to cybersecurity threats to ESG reporting obligations — are entering scope faster than most audit functions can hire for. And every CFO conversation ends in the same place: what is this costing us?
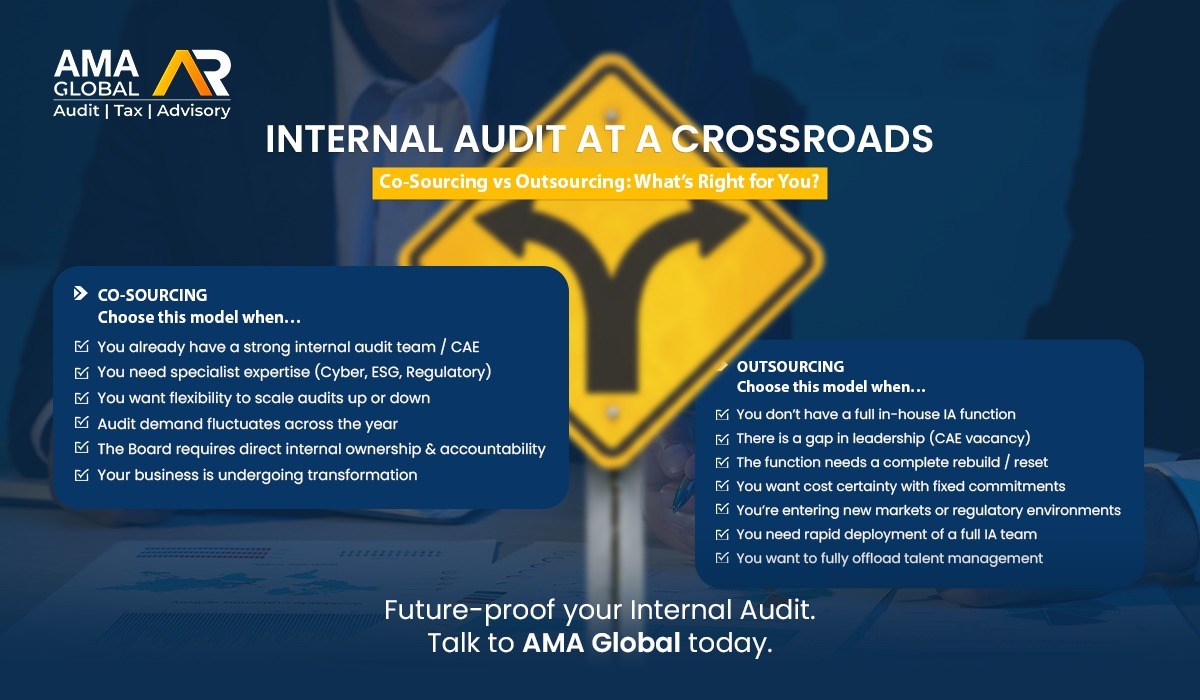
The organisations that will win are not the ones that simply cut harder or hire more. They are the ones that choose the right operating model at the right time. That choice, put plainly, comes down to co-sourcing or outsourcing — and the stakes of getting it wrong have never been higher.
Why this Conversations cannot wait?
Four forces are converging simultaneously, and internal audit sits at the centre of all of them.
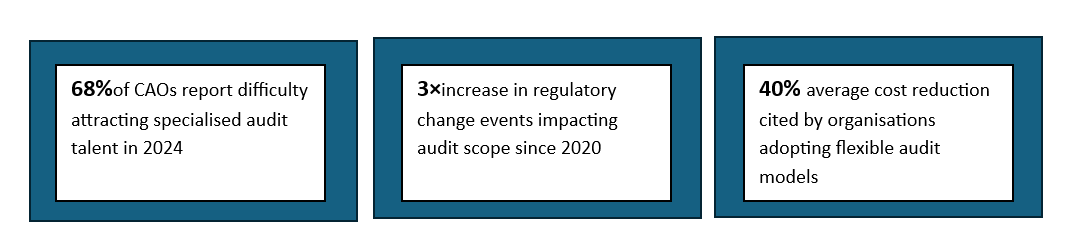
Cost Pressure Is Relentless
Finance and operations leadership are applying downward pressure on every departmental budget. Internal audit, historically shielded by its governance function, is no longer immune. Leaders are being asked to demonstrate ROI, reduce per-audit cost, and justify full-time equivalent headcount against an increasingly variable workload. The financial case for a fixed-cost, fully in-house model is eroding.
Regulatory Complexity Is Accelerating
From DORA in financial services to evolving ESG disclosure mandates, anti-bribery enforcement, data privacy laws, and AI governance frameworks — the regulatory surface area that audit must cover is expanding at pace. No single internal team can maintain genuine expertise across all of it. The cost of non-compliance has never been higher, and regulators are watching more closely than ever.
Emerging Risks Are Outpacing Traditional Coverage
Cyber risk, third-party and vendor ecosystems, algorithmic bias, climate-related financial risk, geopolitical supply chain exposure — these are not theoretical future concerns. They are live audit issues today. Yet most internal functions lack the specialist capability to assess them with credibility. The gap between the risk landscape and audit coverage is widening, and boards are beginning to notice.
Uncertainty & Workforce Volatility
Mass layoffs across technology, financial services, and professional services have left audit departments hollowed out — often losing institutional knowledge that took years to build. At the same time, the surviving teams face heavier workloads, higher scrutiny, and board expectations that have not diminished one iota. The talent pipeline is stressed. Retention is expensive. And flexibility has become a strategic necessity, not a luxury.
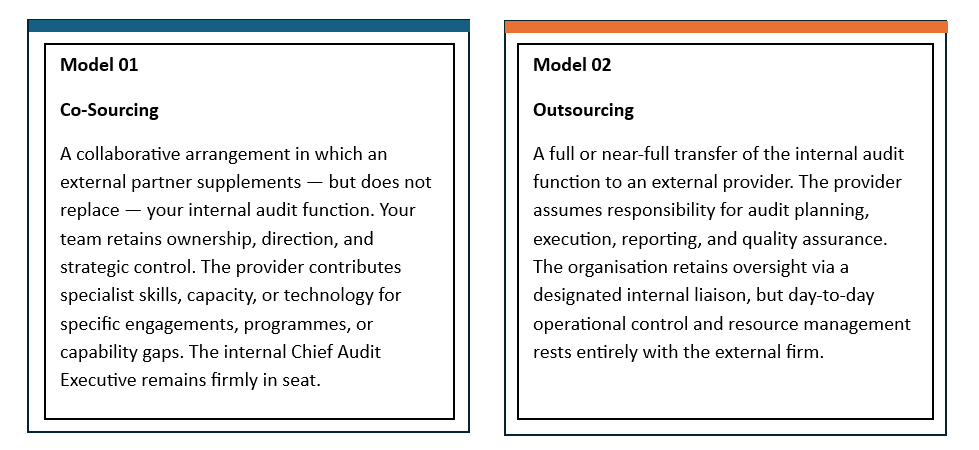
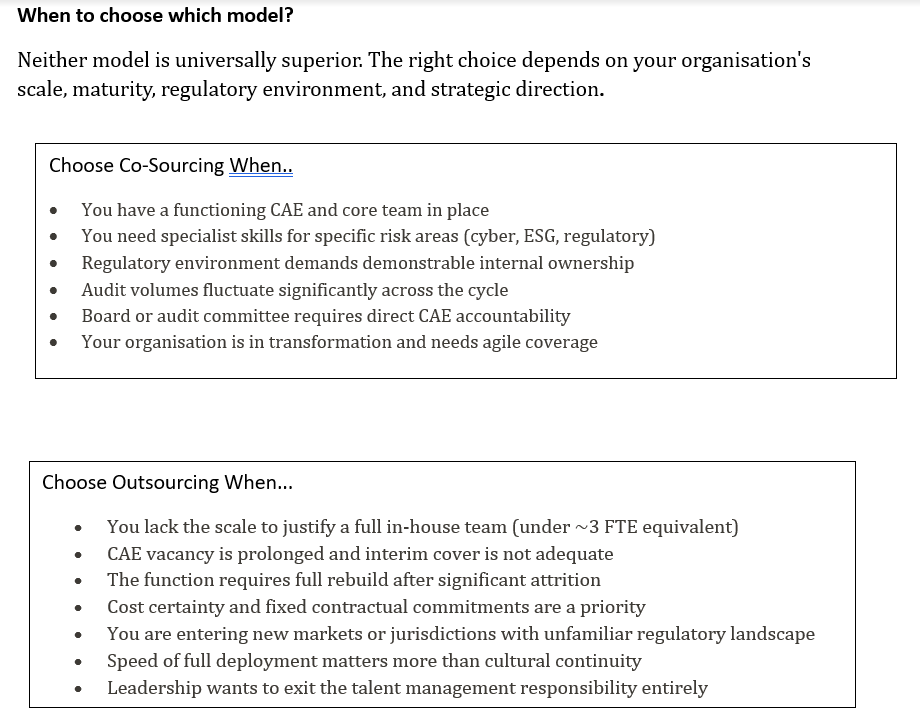
Two Models. One Decision. Get It Right
Before choosing, leadership must understand precisely what each model delivers — and what it demands in return.
How AMA can helps you navigate this decision?
- Co-Sourcing Partnerships
- Full Outsource Model
- Diagnostic & Design
- Transition & Change Support
- Specialist Capability Deployment
- Quality Assurance Reviews
AMA brings deep expertise in designing, deploying, and managing both co-sourcing and fully outsourced internal audit arrangements — tailored to your sector, scale, and strategic objectives.
📩 Contact AMA Global today to learn more about our services or to request a proposal.
Frequently Asked Questions
- Will Outsourcing or Co-Sourcing compromise our audit independence?
Independence is a function of objectivity and structural design — not simply whether staff are employed or contracted. Both models, when properly governed, can fully satisfy IIA independence standards and regulatory expectations. The critical factor is ensuring the provider has no conflicting advisory or consulting relationships with the same entity, that reporting lines to the audit committee are direct and unimpeded, and that the scope and terms of engagement are disclosed appropriately.
- How is sensitive company data protected?
Sensitive data is protected through a combination of contractual, technical, and operational controls. These include signed confidentiality agreements (NDAs), restricted access based on roles, secure data transfer protocols, and adherence to firm-wide information security policies. Access is provided strictly on a need-to-know basis, and all data handling aligns with applicable regulatory and data protection requirements.

Monish Mohan is a versatile and accomplished Auditor, VAT Consultant, Finance and Accounts Professional offering over 18 years of experience in UAE VAT, Audit & Assurance, Finance management Advisory & Accounting & bookkeeping.

